- Home
- About
- Technologies
- Courses
- Microsoft
-
EC-Council
- CSCU: Certified Secure Computer User
- CND: Certified Network Defender
- CEH: Certified Ethical Hacker
- CPENT: EC-Council Certified Penetration Tester
- CNDA: Certified Network Defence Architect
- LPT: Licensed Penetration Tester
- ECES: Certified Encryption Specialist
- CIH: Certified Incident Handler
- CHFI: Computer Hacking Forensic Investigator
- More EC-Council courses >>
- CompTIA
-
Microsoft Azure
- AZ-900 Microsoft Azure Fundamentals
- AZ-104 Microsoft Azure Administrator
- AZ-204 Developing Solutions for Microsoft Azure
- AZ-300 Microsoft Azure Architect Technologies
- AZ-400 Microsoft Azure DevOps Solutions
- AZ-500 Microsoft Azure Security Technologies
- DP-200 Implementing an Azure Data Solution
- AI-100 Designing and Implementing Azure AI Solution
- More Azure courses >>
- Microsoft 365
- Combo Courses
- Firewall
- RedHat
- AWS Cloud
- Google Cloud
- Customized Trainings
- View All courses
- Offer
- SERVICES
-
Training & Certifications
- EC Council trainings
- Microsoft trainings
- Google Cloud trainings
- Azure & AWS trainings
- CompTIA trainings
- COMBO trainings
Business Solutions
- Cyber Security and Audit
- IT Consultancy
- Cloud Services
- VDI - App and Desktops
- On Demand IT Services
- Application Development
Our Solutions
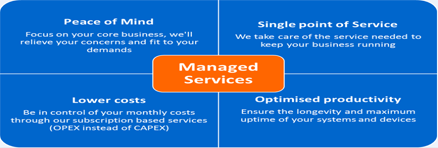
We helps companies in diverse sectors to deploy solutions for Cloud computing, virtualization, mobility, and networking.
-
- Resources
-
Tips & Tricks
- Outlook tips
- Citrix optimizer
Video
- ShareFile overview
- Citrix Cloud
- VMware Edge
How to Install
- Server 2019
- VMware ESXi 6.5
Tutorial
- Exchange server
- Citrix NetScaler
- Network Security
Webinars
- Citrix webinars
- Microsoft events
- VMware webcasts
- AWS webinars
News Updates
- Security related news
-
- Contact